Cool Tips About How To Control Phishing

While most do a decent job at blocking spam and phishing attempts, there may still be a few that slip through the.
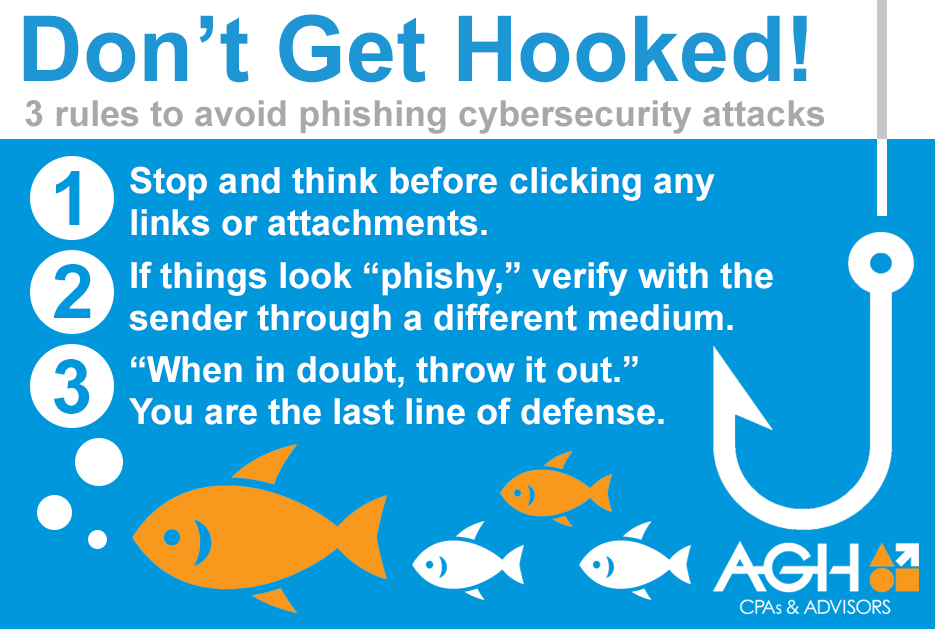
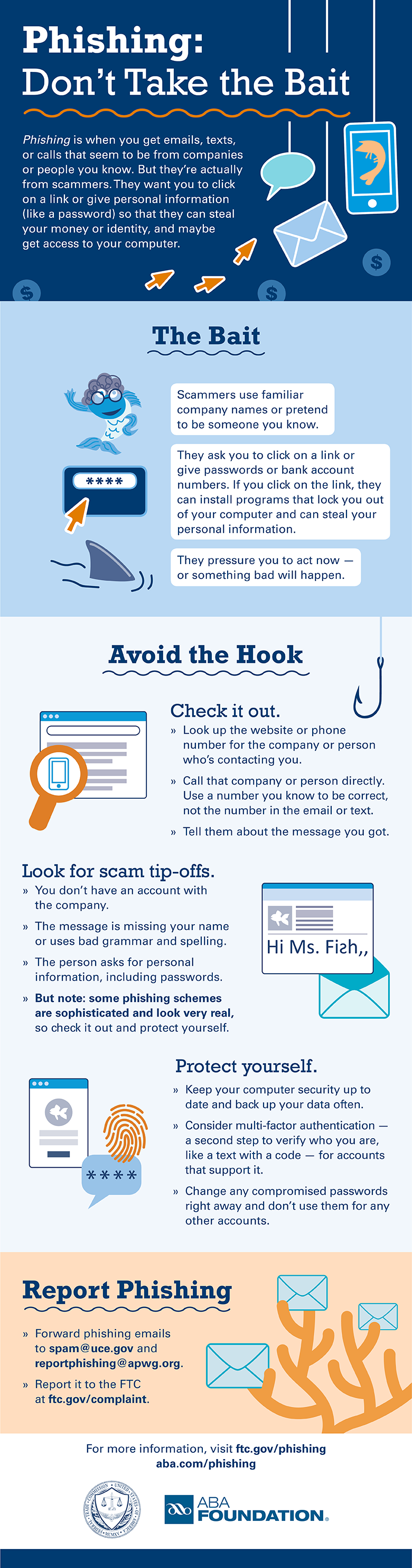
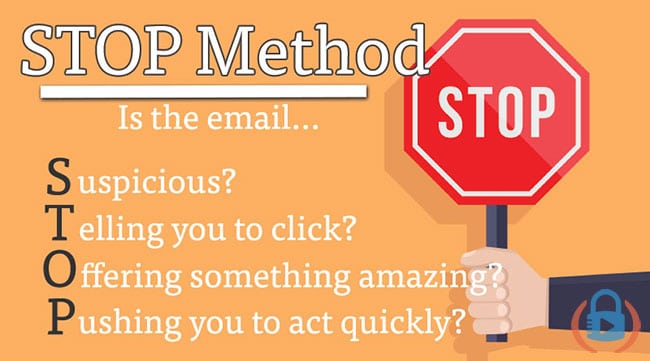
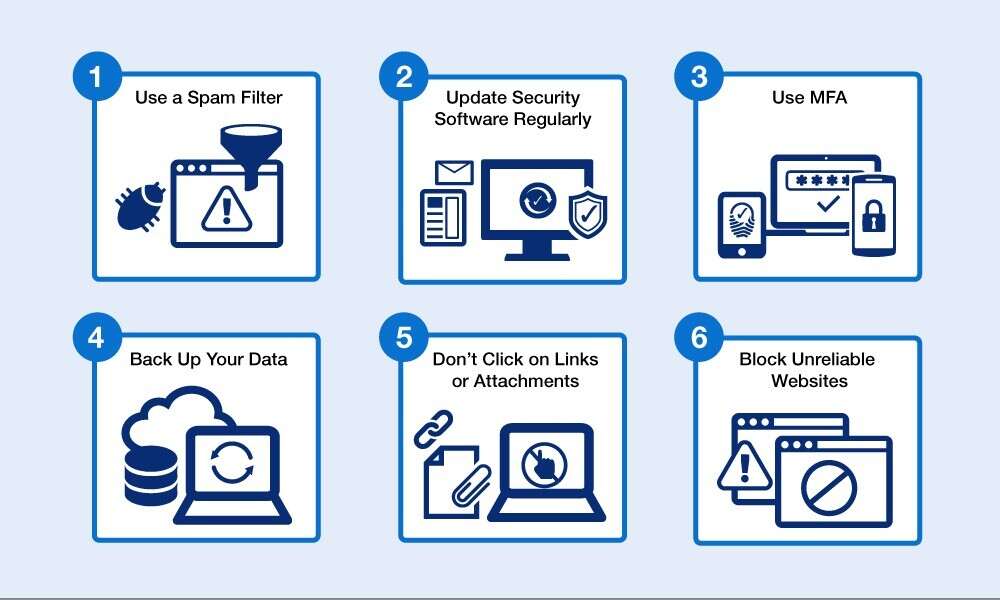
How to control phishing. While in the suspicious message, select report message from the ribbon, and then select. Fortunately, defending against well researched and expertly written phishing emails is not difficult. It’s important to use strong firewalls and updated security filters to block access to any dangerous or illegitimate sites (the same goes for downloads, etc.).
Most software solutions that deal with malware and. Select the arrow next to junk, and then select phishing. If a recipient's account was compromised.
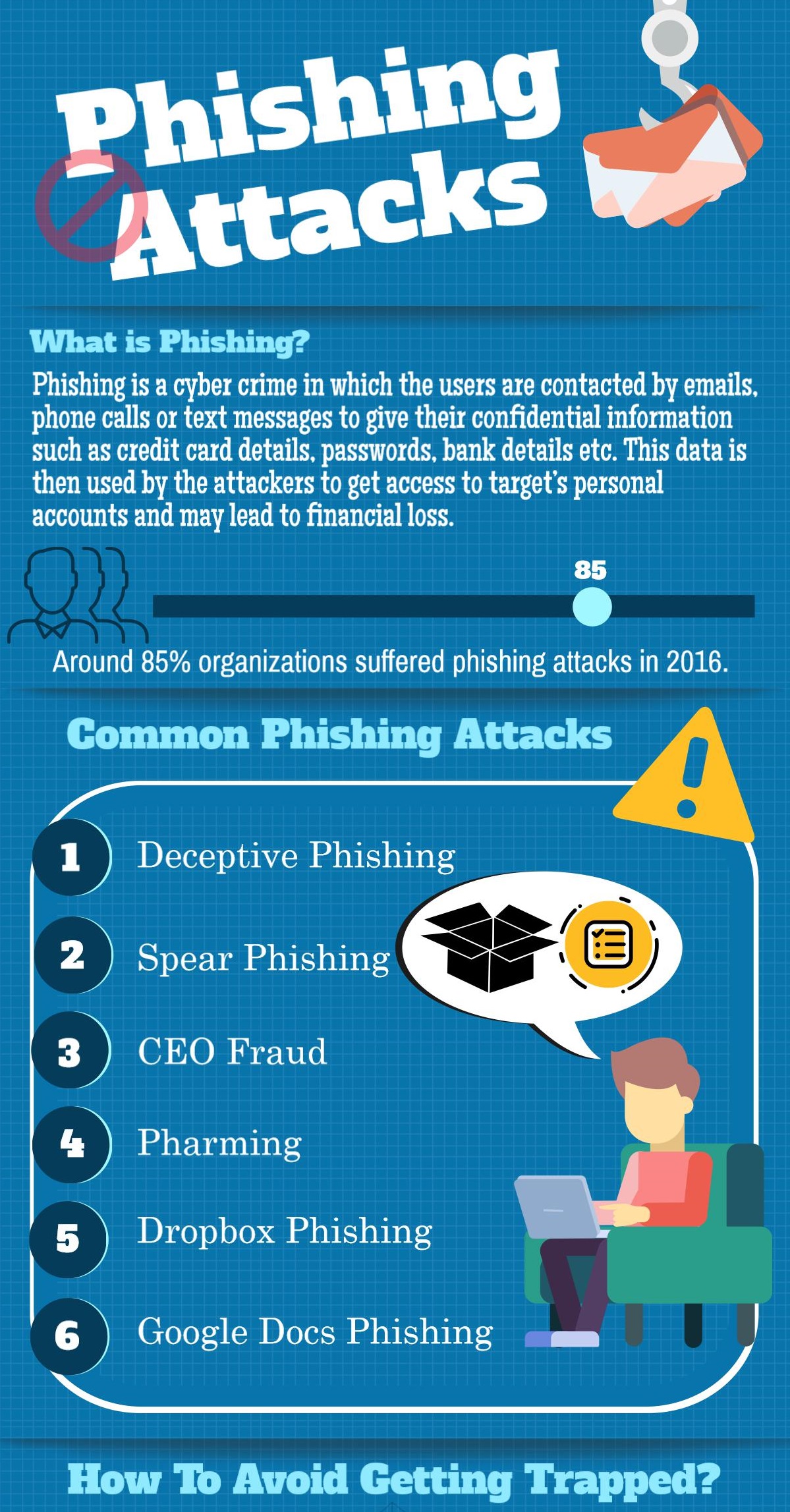
Block consent phishing emails with microsoft defender for office 365 by protecting against phishing campaigns where an attacker is impersonating a known user in the. If you have disclosed sensitive information in a phishing attack, you should also contact one of the three major credit bureaus and discuss whether you need to place a fraud alert on your. Below, we discuss five effective techniques to keep phishing attacks at bay.
The first step you should take is to check your email provider’s settings. Time to go phishing with gophish. Beyond spam filters, there are steps that users should take to avoid becoming a victim of a phishing attack.
Use security antivirus and other appropriate security software on. Don’t click on suspicious links if everyone were careful about the links they clicked on, phishing would.









.jpg)


